Active and Passive Attacks
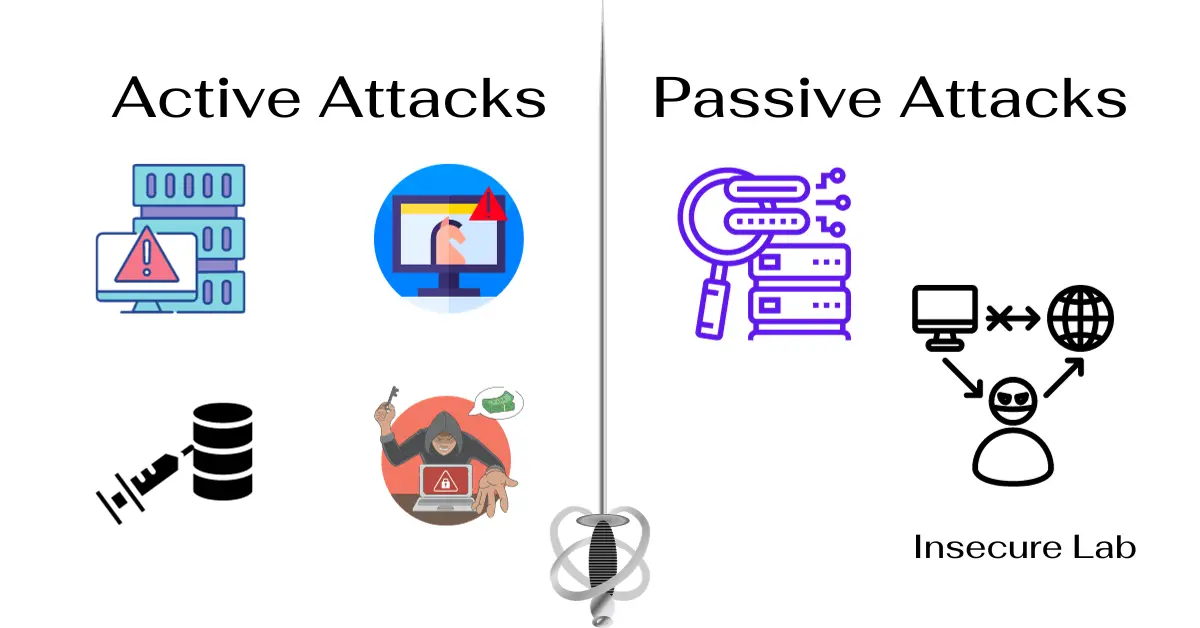
Table of Contents
In this ethical hacking guide, we will explore active and passive attacks. We will look at their definitions, types, examples, and differences in cyber security.
Active Attacks
Active attacks involve actions where the attacker attempts to alter system resources or influence their operation. These attacks are often direct and aggressive. They aim to manipulate or destroy data, disrupt services, or gain unauthorized access.

Here are some common types of active attacks, including examples:
1. DoS and DDoS Attacks
Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks overwhelm a system, server, or network. They send too much traffic to these resources. This makes it hard for real users to access the service.
Example:
A surge of traffic from multiple sources floods the website, causing it to crash and become inaccessible to users.
2. Man-in-the-Middle (MitM) Attack
In a MitM attack, an attacker intercepts and potentially alters the communication between two parties without their knowledge. This allows the attacker to eavesdrop on or manipulate the transmitted data.
Example:
An attacker intercepts and modifies messages between a user and their bank, potentially stealing login credentials or manipulating financial transactions.
3. Malware Attacks
Malware attacks involve infiltrating systems with viruses, worms, trojans, or ransomware to compromise data or disrupt operations.
Example:
A user unknowingly downloads and executes malware, allowing the attacker to control their computer remotely.
4. SQL Injection Attack
In a SQL injection attack, an attacker puts harmful SQL code into a database query. This lets them access, change, or delete data from a website or web application.
Example:
An attacker inserts malicious code into a web form, allowing them to extract sensitive information from a vulnerable database.
5. Cross-Site Scripting (XSS) Attack
An XSS attack involves injecting malicious scripts into web pages, which are then executed by unsuspecting users, potentially stealing their data or session cookies.
Example:
An attacker puts a script in the comment section of a website. When other users read the comments, someone steals their data.
Passive Attacks

Passive attacks involve monitoring or eavesdropping on systems and networks without altering the content. The primary goal is to intercept data transmission and extract valuable information without detection. Someone may later use the information collected for malicious purposes, such as identity theft, espionage, or further active attacks. These attacks are covert and do not alter the data, making them difficult to detect.
Here are some common types of passive attacks, including examples:
1. Eavesdropping
Eavesdropping involves the unauthorized interception of data transmitted over a network, potentially leading to data theft or privacy violations.
Example:
An attacker uses a packet sniffer to capture unencrypted network traffic and obtain usernames and passwords.
2. Packet Sniffing
In a packet sniffing attack, an attacker captures and analyzes network packets to extract information about the content and structure of the data being transmitted.
Example:
An attacker uses a packet sniffer to intercept and examine packets containing sensitive financial data.
3. Traffic Analysis
By analyzing the volume and patterns of data traffic between specific entities, potentially sensitive information can be exposed without access to the actual content.
Example:
An attacker monitors the frequency and timing of a user's login attempts to deduce their work schedule and habits.
Active Attack Vs Passive Attack
Difference Between Active Attack and Passive Attack
This table provides an overview of the key differences between active and passive attacks on various aspects of cybersecurity.
| Aspect | Active Attack | Passive Attack |
|---|---|---|
| Definition | Active attacks involve altering or destroying data or affecting system operations. | Passive attacks involve monitoring or eavesdropping on communications without altering the data. |
| Detection Difficulty | Easier to detect due to the alteration of data or system behavior. | Harder to detect as they don’t involve direct alteration of data. |
| Purpose | To inflict harm or extract information by altering system functionality or data. | To obtain information without affecting system resources or data integrity. |
| Examples | Denial of Service (DoS) attacks, Man-in-the-Middle (MITM) attacks, session hijacking, and data modification. | Eavesdropping, traffic analysis, monitoring of unsecured communications. |
| Impact | Can cause immediate and significant damage or disruption to systems or data. | Typically no immediate damage but poses long-term risks such as privacy breaches or future attacks. |
| Countermeasures | Firewalls, intrusion detection/prevention systems, strong authentication mechanisms. | Encryption, strong network security policies, secure communication protocols. |
| Intent | Often malicious with intent to harm or exploit. | Could be for malicious purposes like spying or for benign purposes like network management and monitoring. |
| Visibility | Visible in terms of effects (e.g., system crashes, altered data). | Invisible in terms of effects, as it involves silently capturing or monitoring data. |
| Required Skills | Generally requires more sophisticated skills to execute as it involves breaking into systems or altering data. | Requires less technical skill as it often involves just listening to or capturing data passing through the network. |
| Response Urgency | Requires immediate response to prevent or mitigate damage. | May not require immediate action but necessitates long-term security measures to protect data privacy. |
| Common Environments | Common in environments where data or system integrity is critical, like financial or military systems. | Common in any environment, particularly where data is transmitted over insecure or unencrypted channels. |
| Prevention Difficulty | More challenging to prevent as it requires robust security measures against a wide range of attack vectors. | Easier to prevent with the use of encryption and securing communication channels. |
Summary
These attacks represent distinct approaches that malicious actors employ to compromise systems, networks, and data. Active attacks are disruptive and more easily detectable, whereas passive attacks are stealthy and more challenging to spot.
Employing a combination of technical and educational strategies is vital for prevention and mitigation. As cyber threats evolve, staying informed and adaptable is crucial for maintaining robust security in an increasingly digital world.
