Intrusion Detection System (IDS)
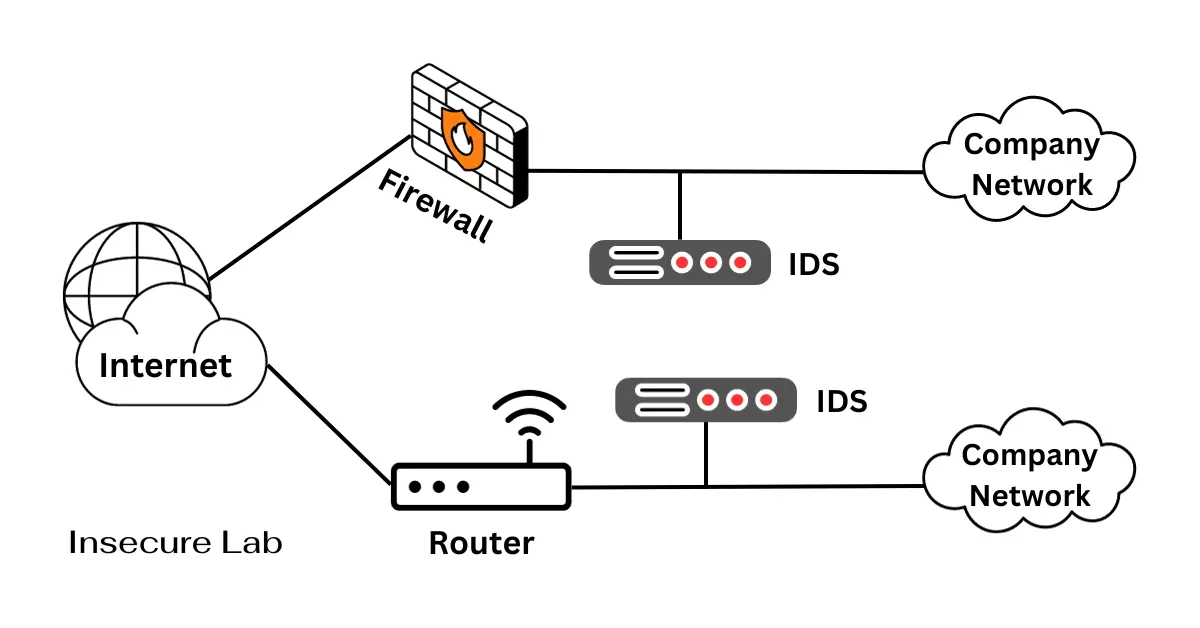
Table of Contents
This guide explains what an intrusion detection system is, IDS vs IPS, network IDS vs host IDS, how IDS works, benefits, limitations, and where it fits in cybersecurity defense.
Quick Answer
An intrusion detection system (IDS) monitors network or host activity for suspicious behavior, policy violations, malware indicators, or attack patterns. It alerts defenders so they can investigate threats, while an IPS can additionally block or prevent selected traffic.
What is Intrusion Detection System?
Intrusion detection system (IDS) is a software application or hardware device that monitors a network or system for malicious activities or policy violations. Any suspicious activity or breach detected is typically either reported to an administrator or collected centrally using a security information and event management (SIEM) system.
The primary goal of an IDS is to protect digital assets from a number of threats, including:
1. Unauthorized Access
Preventing unauthorized users from gaining access to sensitive data or systems.
2. Malware Detection
Identifying and mitigating the effects of malicious software, such as viruses, worms, and ransomware.
3. Denial-of-Service (DoS) Attacks
Detecting and mitigating DoS attacks that overwhelm a system or network, rendering it unavailable.
4. Anomalous Behavior
Recognizing abnormal patterns or activities that may indicate an intrusion attempt.
5. Data Exfiltration
Detecting and preventing the unauthorized transfer of data outside the organization.
IDS vs IPS
An IDS observes activity and raises alerts for analysts, while an intrusion prevention system (IPS) can also block or reject suspicious traffic automatically. Many security programs use both: IDS for visibility and investigation, IPS for inline prevention where false positives are carefully managed.
IDS also supports related controls such as honeypots, firewalls, SIEM tools, and DoS attack monitoring.
Types of Intrusion Detection Systems
There are two primary types of IDS:
1. Network-Based Intrusion Detection Systems (NIDS)
Network-Based Intrusion Detection Systems are deployed at the network perimeter, monitoring the traffic passing through the network. They analyze network packets, looking for suspicious patterns, known attack signatures, or anomalies that deviate from established baselines.
NIDS can be further categorized into two subtypes:
1) Signature-Based NIDS
These systems rely on a database of known attack signatures to identify malicious activities. When incoming traffic matches a signature, the NIDS triggers an alert. While effective against known threats, they may miss zero-day attacks.
2) Anomaly-Based NIDS
These systems establish a baseline of normal network behavior and raise alerts when deviations occur. While more adept at detecting novel threats, they may produce false positives if the baseline is not accurately set.
2. Host-Based Intrusion Detection Systems (HIDS)
Host-Based Intrusion Detection Systems operate on individual hosts or endpoints, closely monitoring activities within the operating system and applications. They are especially useful for detecting insider threats and attacks that originate from within the organization.
HIDS can also be categorized into two subtypes:
1) System Call-Based HIDS
These systems monitor system calls and application interactions, looking for deviations from expected behavior. They can detect unauthorized access and software vulnerabilities exploitation.
2) Log-Based HIDS
Log-Based HIDS analyze system and application logs, searching for unusual patterns or events. They are valuable for detecting unauthorized access and improper configuration changes.
How Intrusion Detection Systems Work?
The functioning of an Intrusion Detection System involves a series of steps:
Step-1: Data Collection
The IDS collects data from various sources, such as network packets, system logs, and event records.
Step-2: Preprocessing
The collected data undergoes preprocessing to filter out irrelevant information and format it for analysis.
Step-3: Analysis
In this phase, the IDS applies detection algorithms to the preprocessed data. For signature-based systems, it compares network traffic or system activities against a database of known attack signatures. Anomaly-based systems compare data against established baselines or statistical models to identify deviations.
Step-4: Alert Generation
When the IDS detects suspicious or malicious activity, it generates alerts. These alerts can vary in severity, and they may trigger responses such as logging the event, notifying system administrators, or even initiating automated countermeasures.
Step-5: Response
Depending on the configuration, an IDS can trigger various responses, including blocking network traffic from suspicious sources, isolating compromised hosts, or initiating incident response procedures.
Challenges and Limitations
1. False Positives and Negatives
IDS can produce false positives, triggering alarms for legitimate activities. Conversely, they may also miss sophisticated attacks, leading to false negatives.
2. Signature Dependency
Signature-based IDS are reliant on a database of known attack patterns. They struggle to detect zero-day attacks or novel threats that lack predefined signatures.
3. Complexity of Network Traffic
Analyzing the sheer volume and complexity of network traffic can be overwhelming. IDS may struggle to keep up with high-speed networks and encrypted traffic.
4. Evasion Techniques
Attackers constantly develop evasion techniques to bypass IDS, making it a cat-and-mouse game between security professionals and threat actors.
5. Resource Consumption
HIDS, in particular, can consume significant system resources, potentially impacting system performance.
Where IDS Fits in a Security Program
IDS is most useful when alerts are connected to asset inventory, log review, incident response, endpoint protection, and network segmentation. For practical learning, compare IDS with honeypot systems, whitelist vs blacklist controls, and broader network security testing.
Summary
Intrusion Detection Systems play a vital role in safeguarding digital assets from a wide range of cyber threats. Their ability to monitor network traffic, system logs, and application activities makes them an essential component of modern cybersecurity strategies. While they do have limitations, ongoing advancements in technology and a proactive approach to threat detection are steadily improving their effectiveness.
As the cybersecurity landscape continues to evolve, Intrusion Detection Systems will remain a crucial tool in the ongoing battle to protect our digital frontiers. Organizations that invest in robust IDS solutions and stay updated with emerging trends will be better equipped to defend against the ever-evolving threat landscape.
