Ping of Death Attack
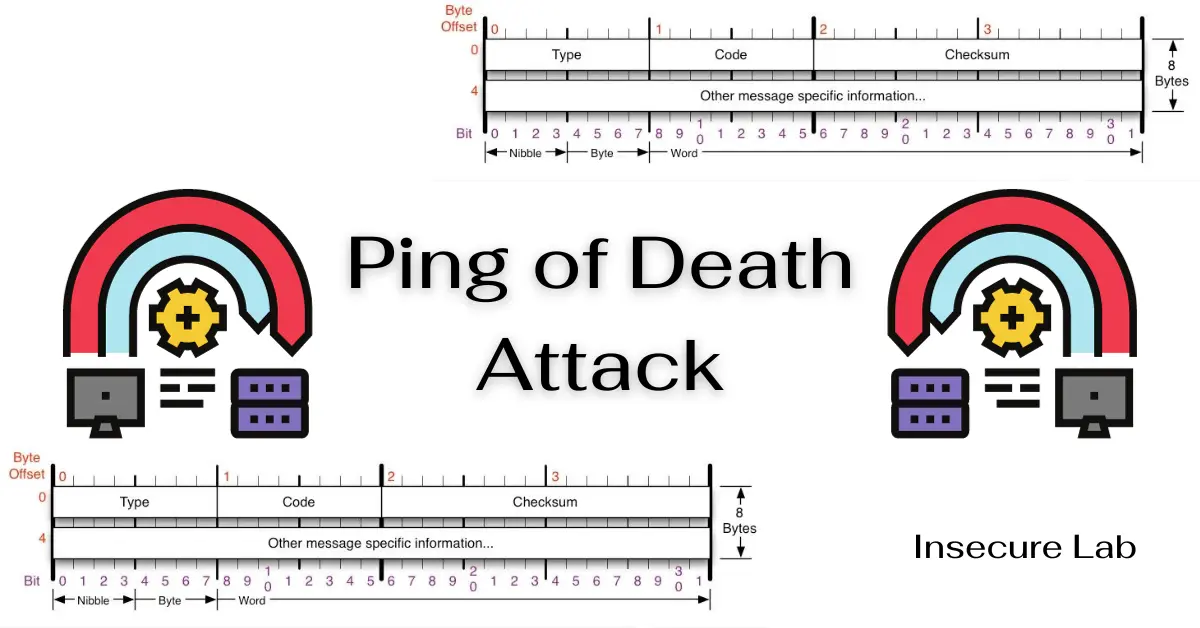
Table of Contents
In this guide we will learn about the Ping of Death attack, its history and different types. We will also discuss about the detection techniques and effective prevention methods for these types of DoS attacks in cyber security.
What is Ping of Death?
The Ping of Death is a type of Denial of Service attack that targets networked devices and computer systems by sending malformed or oversized Internet Control Message Protocol (ICMP) packets. ICMP is a fundamental protocol used for network diagnostics and error reporting. When a device receives an ICMP Echo Request packet (commonly known as a ping), it responds with an ICMP Echo Reply packet. Hackers exploit the Ping of Death attack by crafting ICMP packets that are excessively large, causing the target system to crash or become unresponsive.
The Anatomy of a Ping Packet
To understand how the Ping of Death attack works, it's essential to grasp the structure of an ICMP packet. Typically, an ICMP Echo Request packet consists of an ICMP header and a payload (data section). The header contains essential information, including the type of ICMP message, a checksum for error-checking, and a unique identifier.
The attacker manipulates the packet by making the payload larger than the maximum allowed size. This triggers a buffer overflow or other vulnerabilities in the target system, leading to instability or a complete crash.
History of Ping of Death Attacks
The Ping of Death attack dates back to the early days of the internet. It gained notoriety in the late 1990s when it was used to exploit vulnerabilities in various operating systems, including Windows and Linux. During this time, many systems were not properly equipped to handle excessively large ICMP packets, making them susceptible to this type of attack.
The term "Ping of Death" itself became widely recognized during these early years of cyberattacks. While advancements in network security have mitigated some of the vulnerabilities that made these attacks possible, Ping of Death attacks still serve as a valuable case study in understanding the principles of network exploitation.
Exploiting Network Vulnerabilities
The Ping of Death attack primarily exploits two types of vulnerabilities in target systems:
1. Buffer Overflow Vulnerabilities
When an oversized ICMP packet is received, it can overflow the buffer allocated for processing ICMP packets. This overflow can lead to unpredictable behavior, including system crashes or the execution of malicious code.
2. Protocol Non-Compliance
Some older or poorly configured network devices may not adhere to the ICMP protocol's specifications, allowing them to mishandle oversized packets. This non-compliance can result in system instability or crashes.
Modern Variations of PoD Attacks
Some of the common variations are:
1. Distributed Ping of Death
Instead of launching the attack from a single source, hackers use a botnet, a network of compromised devices, to send a coordinated barrage of oversized ICMP packets. This makes the attack more challenging to detect and mitigate.
2. Fragmented Ping of Death
In this variant, the oversized ICMP packet is fragmented into smaller packets, with each fragment staying within the maximum allowable size. When the target system reassembles these fragments, it may mishandle the oversized packet, leading to a successful attack.
3. Amplified Ping of Death
Attackers send Ping of Death packets to vulnerable servers with IP spoofing, making the response packets larger than the original requests. This technique can magnify the impact of the attack.
As network security has improved, attackers have adapted and developed new techniques. Modern variations of Ping of Death attacks include:
Detection Techniques
Detecting Ping of Death attacks requires network administrators to be vigilant and employ a variety of tools and techniques:
1. Intrusion Detection Systems (IDS)
An intrusion detection system can monitor network traffic for signs of anomalous ICMP packet sizes and patterns, triggering alerts or blocking traffic when suspicious activity is detected.
2. Packet Inspection
Deep packet inspection tools can analyze network traffic and identify oversized ICMP packets that deviate from standard specifications.
3. Logging and Monitoring
Maintaining detailed logs of network traffic and regularly monitoring them can help identify unusual patterns or repeated ICMP requests from the same source.
Prevention Methods
Preventing Ping of Death attacks involves a combination of best practices, network configurations, and security measures:
1. Patching and Updating
Keep all network devices and operating systems up to date to patch known vulnerabilities that Ping of Death attacks exploit.
2. Firewall Rules
Configure firewalls to block oversized ICMP packets and ICMP traffic from untrusted sources, reducing the attack surface.
3. Intrusion Prevention Systems (IPS)
Deploy IPS solutions that can detect and block Ping of Death attacks in real-time.
4. Network Segmentation
Isolate critical network segments to minimize the impact of a successful attack on the entire network.
5. Rate Limiting
Implement rate limiting for ICMP traffic to prevent an excessive number of ICMP requests from overwhelming the system.
6. Security Awareness
Educate network administrators and users about the dangers of Ping of Death attacks and encourage safe online practices.
Summary
The Ping of Death attack, though originating from the early days of the internet, remains a viable threat to networked systems. Understanding its history, mechanics, and modern variations is crucial for effective defense. By following best practices, employing network security measures, and staying vigilant, organizations can significantly reduce their vulnerability to Ping of Death and other similar threats in today's ever-evolving cybersecurity landscape.
