Table of Contents
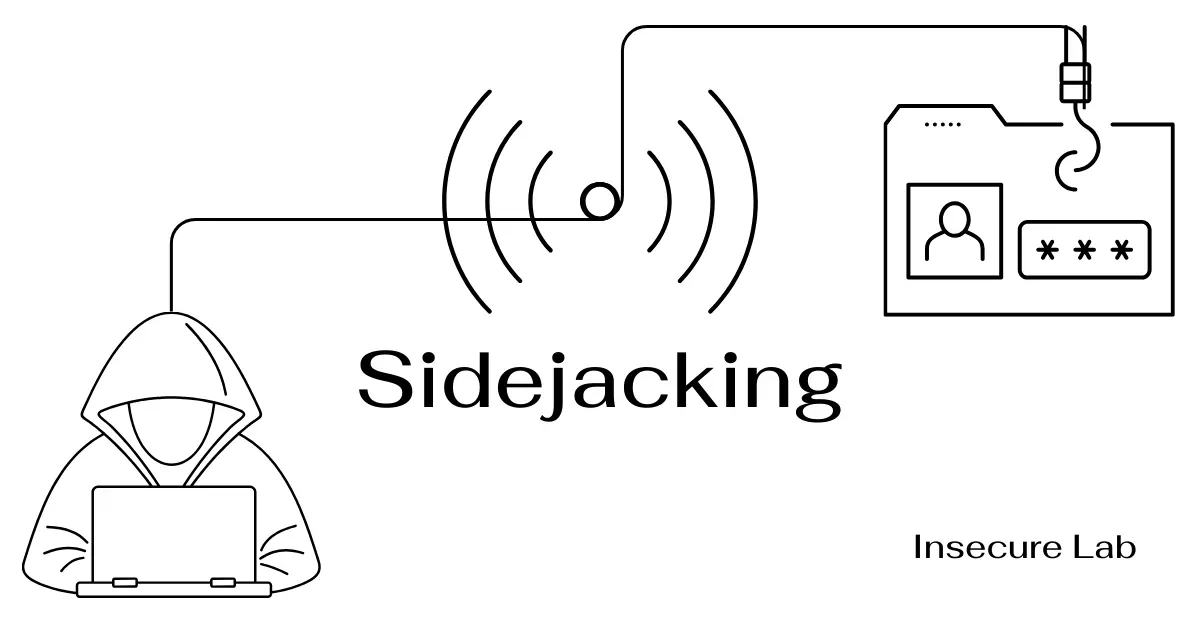
This ethical hacking guide explains what sidejacking is, how session sidejacking works, an example of sidejacking attack, and its prevention in cyber security.
What is Sidejacking?
Sidejacking is a type of session hijacking attack that involves sniffing network traffic to find and capture session tokens, which are often transmitted insecurely. This attack uses unencrypted communications to intercept session tokens, allowing attackers to impersonate victims on web applications.
How Sidejacking Works?
In a sidejacking attack, when a user logs in to a website using an unsecured network connection such as public WiFi, their login information and session token (unique ID obtained after successful authentication) is transmitted in plain text (without encryption). This allows an attacker to easily obtain this information using packet sniffing tools. Once the attacker obtains the user’s login credentials or session token they use them to gain unauthorized access to the account.
Steps Involved:
1. Detection
The attacker uses tools like Ferret or Hamster to examine WiFi hotspot traffic, looking for any session tokens sent without proper encryption or with weak encryption.
2. Capture
The attacker uses sniffing tools to capture data packets from WiFi network traffic. The attacker then identifies the session token from the captured data packets by applying his knowledge of how session tokens are generated and transmitted by various target systems.
3. Manipulation
The attacker attempts to insert the captured session token into the communication with the targeted application to confirm the feasibility of the exploit.
4. Exploitation
The attacker leverages the captured session token to perform malicious interactions with the target application while impersonating the victim.
Example of a Sidejacking Attack
Let’s consider a hypothetical example to illustrate a sidejacking attack:
Scenario:
Alice visits a local coffee shop and connects to the free Wi-Fi to access her email account on a website that does not use HTTPS. Bob, an attacker, is monitoring the network traffic using a packet sniffer.
Execution:
Bob captures the packets being sent between Alice’s laptop and the email server. Among these packets, he finds the session cookie that is used to verify Alice to the email server.
Attack:
Bob copies Alice’s session cookie and uses it on his device to log into the email server. Because the session cookie is valid, the server recognizes Bob as Alice and grants him access.
Outcome:
Bob now has access to Alice’s email account without needing her password.
Prevention and Mitigation
Preventing sidejacking involves several layers of security, both from the end users’ perspective and from the web application developers’ side. Some effective preventive measures to reduce the risk of attack include:
1. Use HTTPS
Ensure all web traffic is encrypted by using HTTPS instead of HTTP. HTTPS encrypts the entire communication, thus protecting the transmission of session cookies over the network.
2. Secure Cookies
Web developers should set cookies with the Secure attribute, which ensures they are only sent over encrypted connections. Additionally, the HttpOnly attribute should be used to prevent access to cookie values via client-side scripts.
3. Use VPN in Public Networks
When using public Wi-Fi, utilizing a VPN can add an extra layer of security by encrypting all traffic from a user’s device until it reaches the VPN server, making it much harder for attackers to sniff packets.
4. Session Timeout Management
Web applications should implement automatic session expiration, reducing the risk of session hijacking if a session token were to be stolen.
5. Regularly Clear Cookies
Users should be encouraged to regularly clear their cookies and log out of websites when using shared or public computers.
6. Educate Users
Educating users about the risks of using unsecured networks for accessing sensitive accounts can reduce the risk of sidejacking.
Summary
- Session sidejacking is a significant security threat, especially on insecure networks.
- Session tokens are used in most web applications to authenticate the user without requiring a username and password for every interaction, making them a prime target for attackers.
- Both users and developers should take proactive measures to secure sessions and personal data.
- Awareness, proper security settings, and regular monitoring of session activities are important to protect against sidejacking attacks.