🔍 Search
📥 Subscribe
Denial of Service (DoS) Attack
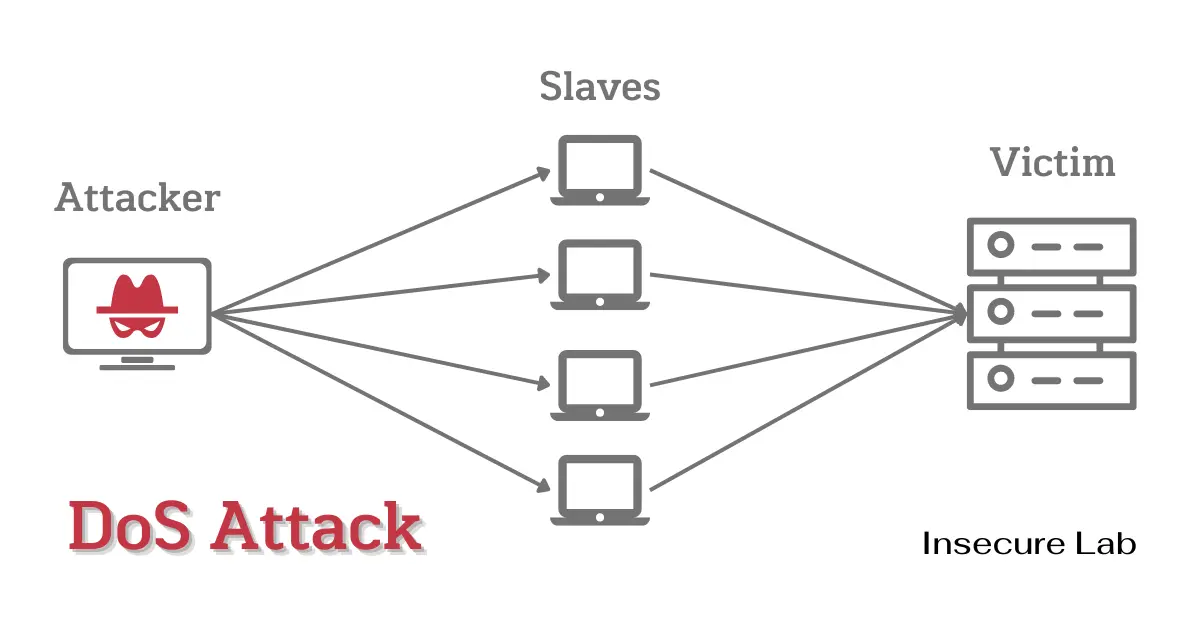
Table of Contents
This ethical hacking guide explains what a denial of service attack is, how it works, types of DoS attacks, prevention and mitigation in cyber security.
What is a DoS Attack?
A Denial of Service (DoS) attack is a malicious attempt to disrupt the normal functioning of a targeted server, service, or network by flooding it with traffic, making it unavailable to legitimate users.
In a DoS attack, the perpetrator does not seek to breach security measures or steal data; instead, the primary goal is to disrupt service. The attacker achieves this by either sending a large number of requests to the target system or by exploiting vulnerabilities in the target system's software to cause it to crash or become unresponsive.
Types of DoS Attacks
DoS attacks come in various forms, each with its own unique characteristics and methods. Here are some of the most common types:
1. Ping of Death Attack
The Ping of Death attack is a specific type of Denial of Service (DoS) attack that exploits vulnerabilities in a computer's network stack or operating system. This attack technique utilizes malformed or oversized Internet Control Message Protocol (ICMP) packets, commonly associated with the "ping" command, to overwhelm the target system.
2. Teardrop Attack
In a Teardrop attack, the attacker sends fragmented packets with overlapping offsets and payloads to the target computer. When the victim computer tries to reassemble the packets, it becomes confused and may crash or freeze.
3. SYN Flood Attack
A SYN Flood Attack exploits the vulnerability in the TCP/IP handshake process by sending a large number of connection requests to the target system. The target system tries to respond to each request, but the attacker does not respond to the target system's response. As a result, the target system's resources are exhausted, and it becomes unresponsive.
4. Land Attack
The Land attack involves sending spoofed packets to the victim computer, with the source IP address and port number set to that of the victim itself. This causes the victim computer to try to establish a connection with itself, resulting in a loop that can cause the computer to become unresponsive or crash.
5. Smurf Attack
In a Smurf Attack, the attacker sends a large number of ICMP echo requests to a network's broadcast address, which is then sent to all devices on the network. The devices on the network then send ICMP echo replies back to the broadcast address, overwhelming the target server with traffic and causing it to become unavailable.
6. UDP Flood Attack
This type of attack involves sending a large number of UDP (User Datagram Protocol) packets to the target system, overwhelming it with traffic and causing it to become unresponsive.
7. HTTP Flood Attack
This type of attack involves sending a large number of HTTP requests to a web server, which can overwhelm the server's resources and cause it to become unresponsive.
8. Slowloris Attack
This type of attack involves sending a large number of HTTP requests to a web server, but slowly and over a long period of time. This ties up the server's resources, preventing it from responding to other requests.
Prevention and Mitigation
Preventing DoS attacks requires a multi-layered approach that includes both technical and procedural measures. Here are some effective strategies:
1. Implement Network Security Measures
-
Firewalls:
Utilize firewalls to filter incoming traffic and block malicious requests. Modern firewalls can identify and block suspicious patterns associated with DoS attacks. -
Intrusion Detection and Prevention Systems (IDS/IPS):
Implement IDS/IPS solutions to monitor network traffic for anomalies and automatically block or alert on suspicious activity. -
Virtual LANs (VLANs):
Segment your network into VLANs to limit the scope of a potential attack and prevent lateral movement by attackers. -
Access Control Lists (ACLs):
Use ACLs to restrict access to critical network resources and only allow trusted devices to communicate with them.
2. Implement Rate Limiting and Traffic Shaping
-
Rate Limiting:
Set up rate limiting policies on routers and switches to restrict the number of requests from a single IP address or user. This can help prevent abuse of your resources. -
Traffic Shaping:
Implement traffic shaping to prioritize and allocate bandwidth for critical services and users, ensuring that essential functions are not disrupted during an attack.
3. Utilize Content Delivery Networks (CDNs)
CDNs distribute traffic across multiple servers and data centers, reducing the impact of DoS attacks. CDNs can absorb the traffic and filter out malicious requests before they reach your infrastructure.
4. Deploy Load Balancers
Load balancers distribute incoming traffic evenly across multiple servers. This not only improves performance but also prevents a single server from becoming overwhelmed during an attack.
5. Regularly Update and Patch Systems
Keep your systems, software, and firmware up-to-date with security patches. Vulnerabilities in outdated software can be exploited by attackers.
6. Develop an Incident Response Plan
Create a comprehensive incident response plan that outlines the steps to be taken in the event of a DoS attack. Ensure that your team knows how to respond quickly and effectively.
Summary
DoS attacks are a significant threat to online services and can cause substantial disruption and financial loss. Understanding the nature of these attacks and implementing effective prevention and mitigation strategies is essential for maintaining the security and reliability of internet services and networks.
